The Two Common API Designs
When building authenticated APIs, developers usually follow one of these two approaches:
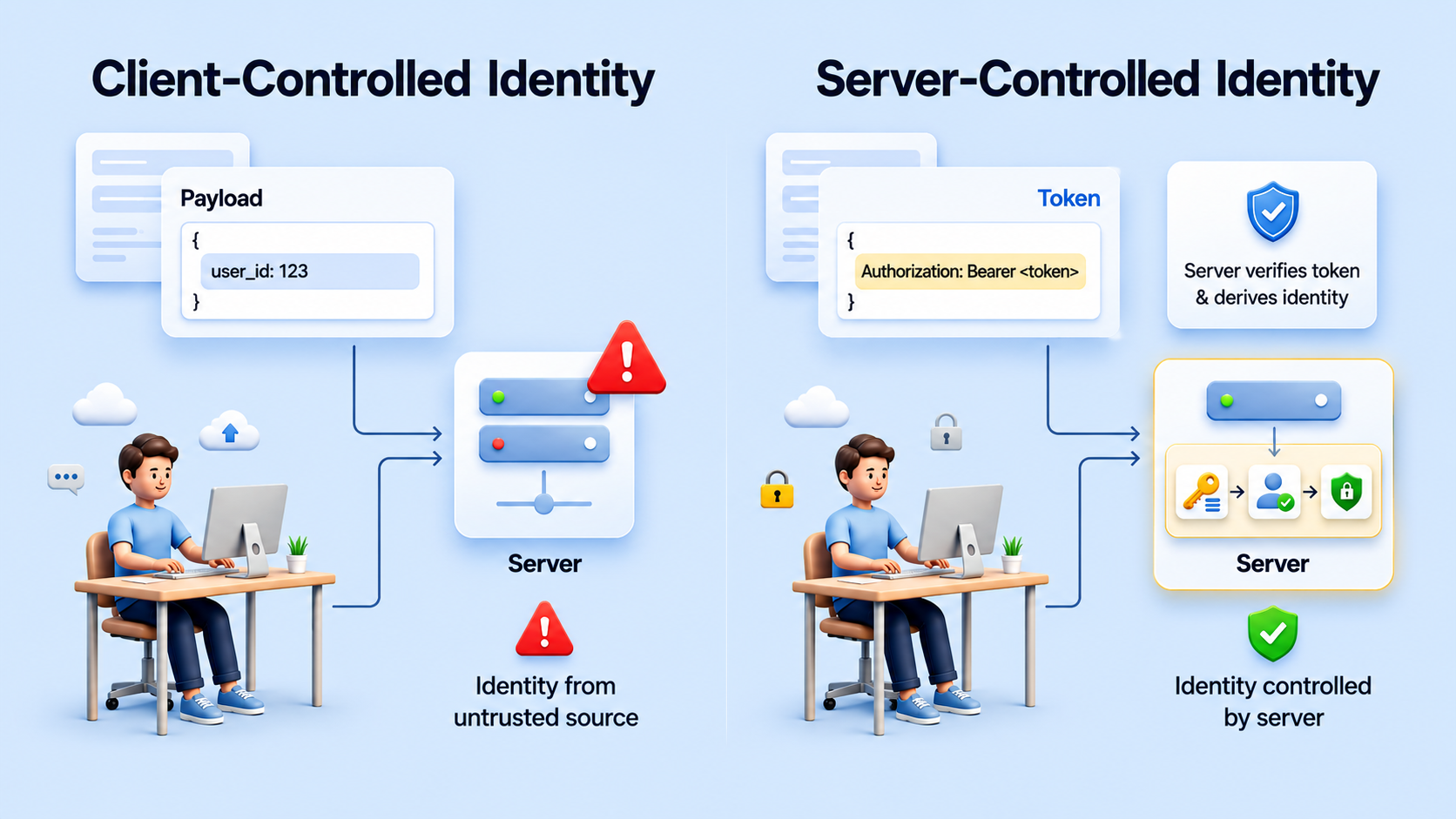
Approach 1 – Client-Supplied Identity
The client sends:
{
"user_id": 42,
"action": "create_order"
}The backend trusts this value.
Approach 2 – Token-Derived Identity
The client sends only the access token:
Authorization: Bearer <JWT>The backend verifies the token and internally extracts the user identity.
The client never controls the user_id.
At first glance, both seem to work. From a security perspective, they are very different.